It’s easy to imagine a hacker breaching an environment using a zero-day exploit but often breaches are from far more mundane reasons. The World Economic Forum’s Global Risks Report found that 95% of cybersecurity issues are a result of human error.
Let’s look at three common Cloud Configuration Management mistakes and how to avoid them.
1. Misconfiguration as Code.
When a team is manually deploying resources to the cloud it creates many opportunities for misconfiguration. Because of this many teams have wisely moved to infrastructure as code tools like Terraform. Infrastructure as code provides many advantages like repeatability, versioning, and the ability to rapidly deploy. This makes it easier to avoid misconfigurations but they can still happen. And now when a misconfiguration makes it through, those advantages can spread the misconfiguration across many resources.
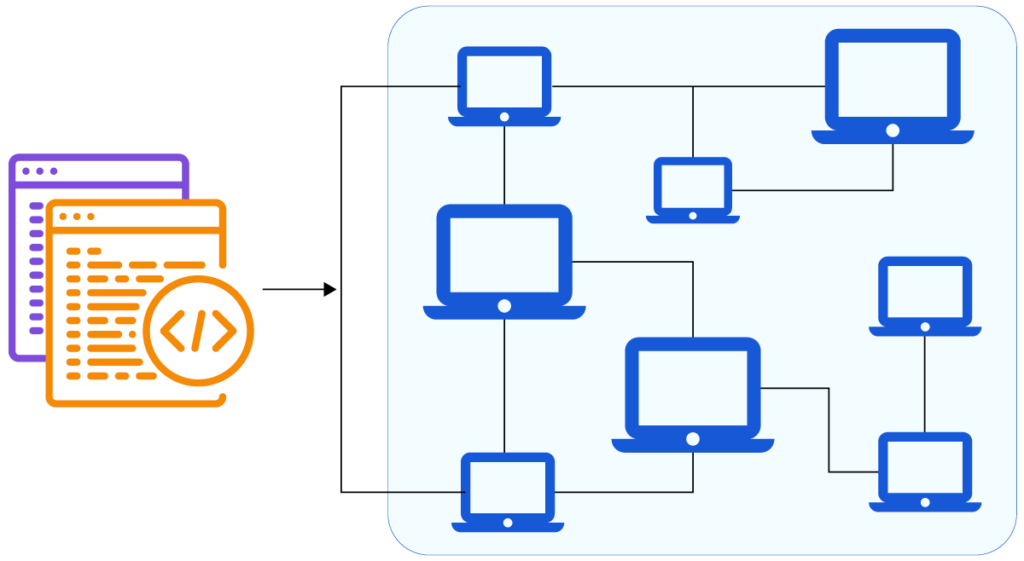
We all can use a second pair of eyes, peer reviewing changes the quality of the code, and therefore the infrastructure improves. Implement peer and programmatic reviews into the deployment process to greatly reduce the risk of misconfigurations making it through.