Security Incident Management (SIM) refers to identifying, managing, and resolving security incidents within an organization’s IT or IOT infrastructure. The primary goal is to minimize the impact of security breaches or incidents such as cyber-attacks, data breaches, unauthorized access, and system vulnerabilities. A recent survey showed that 20% of organizations had six or more security attacks annually and 77% of security leaders anticipated a critical infrastructure breach in the near future.
This article describes each step in the incident management process so you can implement it in your organization and improve the company’s overall cyber security posture.
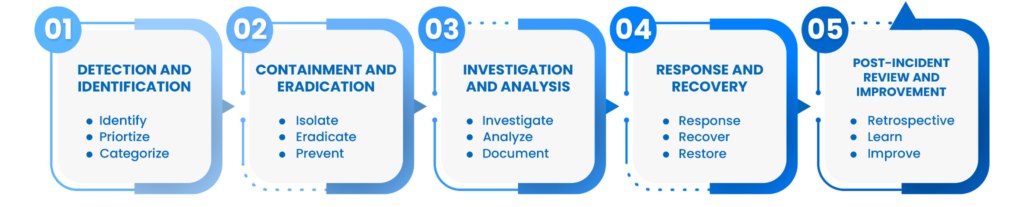
The image shows five Security Incident Management phases covered in this article.
Summary of security incident management phases
| Phase | Description |
|---|---|
| Detection and identification | Identify and categorize security incidents promptly, prioritizing based on severity and potential impact. |
| Containment and eradication | Isolate affected systems and eradicate the root cause to prevent further damage or data loss. |
| Investigation and analysis | Conduct a thorough investigation to understand the incident’s nature, scope, affected systems, and potential data compromise. |
| Response and recovery | Implement a coordinated plan to respond to the incident, recover affected systems, and restore operations. |
| Post-incident review and improvement. | Analyze the incident response process, document findings, and update protocols to enhance future incident response capabilities. |
The rest of this article covers each of these phases in detail.
#1 Detection and identification
This initial step involves a variety of methodologies and tools to collect logs and correlate them with alerts and incidents to detect anomalies or suspicious activities that may indicate a security breach.
Detection mechanisms
Intrusion Detection Systems (IDS) monitor network traffic for signs of unauthorized access, malware, or suspicious patterns. They act as early warning systems and raise alerts when potential threats are detected. Similarly, firewalls analyze incoming and outgoing traffic to present a barrier between trusted internal and untrusted external networks. They apply predefined security rules to filter and block potentially harmful data packets and IP connections.
With the increasing complexity of cyber threats, you can also use dedicated security monitoring tools such as SIEMs, EDR/XDRs, UBA, and cloud security monitoring tools to surveil systems, applications, and user behavior constantly. In cloud-based infrastructure, vulnerability scans are pivotal in identifying weaknesses or misconfigurations within cloud services, unpatched systems, or applications. You gain insights to rectify potential entry points for attackers.
Beyond automated systems, the keen observations and reports from users within an organization can often provide invaluable insights into anomalies or suspicious activities that automated systems might overlook. For example, a well-spotted and reported phishing attack could prevent an APT attack before it even started and save your company time and resources.
Categorization and severity assessment
Security teams categorize the incident based on its type, like a ransomware attack, data breach, unauthorized access, or other cyber threats. You can also categorize on other factors that your organization defines for itself, like
- Threat modeling
- Resource availability
- Criticality of assets
- Potential impact on the organization’s operations,
- Data integrity
- Overall functionality
Categorization helps to understand the specific characteristics of the incident and evaluate the level of urgency and resource allocation so that teams can respond with minimum loss of time. An example table of severity levels is shown below:
| Severity Level | Description | Specific Criteria | Cloud-based example |
|---|---|---|---|
| Low | Low-level incidents typically involve minor security issues with limited to no impact on operations and data. You can resolve them without immediate intervention. |
|
A brute-force attack on a cloud instance without successful authentication. |
| Moderate | Medium-severity incidents are more significant and pose a moderate security risk to the organization’s operations. These incidents may require a timely response but are not considered critical emergencies. |
|
Suspicious successful login to AWS bucket (e.g., impossible location change by the user in a short period). |
| High | High-severity incidents are critical events that require immediate attention. Rapid response and mitigation are essential to minimize the impact. |
|
Real-time DDoS attack on critical cloud infrastructure. |
| Critical | Critical incidents are the highest level of urgency and risk. Immediate and comprehensive response is required to prevent catastrophic consequences. |
|
Data exfiltration from cloud instance over C2 channel. |
Prioritization is pivotal in this phase, enabling organizations to allocate their resources wisely and help reduce alert fatigue. A hierarchy of response urgency is established by categorizing incidents and understanding their severity. Limited resources, whether in terms of time, expertise, or tools, are directed toward addressing the most critical incidents first.
Within your organization, you may already have implemented best-in-class security tools to monitor your cloud environments, like vulnerability scanners, CSPM, DSPM, and application code scanners. Unfortunately, these tools are often used in isolation, and correlating results from these tools is a manually intensive activity. Duplicate, redundant, and out-of-context alert notifications lead to alert fatigue within security operation teams, and critical issues can be missed. To address this, the latest security tools are aggregating findings from the different security tools and using generative AI to apply a risk score and prioritize findings. Critical business context is added by correlating these findings across the different tools. An example of context-based prioritization is correlating the findings of a misconfigured cloud storage account with public access enabled (from your CSPM) and known to contain sensitive data (from your DSPM).

Paladin Cloud’s prioritization dashboard unifies findings from multiple security tools into a single location and uses Generative AI to determine the Top 10 Risks Scores.
Continuous evolution and learning
Moreover, this phase is not static. It evolves as new threats emerge and technologies advance. Continuous improvement in detection mechanisms, improving categorization methods, and adjusting severity assessment frameworks are imperative to stay ahead. Also, the company must record the time it takes to resolve an incident for each severity category. These resolution times quantitatively measure a security operations team’s effectiveness.
#2 Containment and eradication
Containment and eradication are critical in security incident management to cease the incident’s progression and eliminate its effects. This phase requires a swift and decisive response to prevent further harm to an organization’s systems, data, and operations and limit attacker possibilities as much as possible.
Prevent escalation and limit damage
The immediate objective during containment is to prevent the incident from spreading and causing additional harm. This could involve measures such as:
- Quarantine affected systems or network segments to prevent attackers from pivoting among assets or escalating privileges.
- Disable compromised services or applications to cease the incident’s propagation and protect other interconnected systems from being affected.
- Employ stopgap measures or temporary controls to limit the incident’s reach and mitigate its impact while a more permanent solution is devised.
You must tag and name resources appropriately in your cloud systems to distinguish whether it is a test/development/production environment because it would significantly reduce the implementation time for all of those measures. Here is an example of best practices and how to implement them for your Azure infrastructure. For the cloud infrastructure like, for example, SaaS, some of those actions may be the cloud provider’s responsibility and are fully covered by them. Understanding the shared responsibility model is imperative.
Root cause elimination
Once the incident is contained, the focus shifts toward eliminating the root cause. This involves a more in-depth and strategic approach. For example, if the incident requires malware, thorough and systematic removal processes are initiated to eliminate the malicious software from affected systems. EDR/XDR or anti-virus tools would help with that task. You can also:
- Identify and apply necessary security patches to systems or software that might have vulnerabilities exploited in the incident.
- Address weaknesses or flaws in the system’s architecture, configurations, or applications that contributed to the incident.
- Reconfigure systems or networks to prevent a recurrence of similar incidents by fortifying defenses against potential attack vectors.
This step often demands collaboration among various teams, including IT security experts, system administrators, and sometimes external specialists. Decisions required in this stage, for example, assets containment, can disrupt the company’s “business as usual.” However, they are essential to prevent even more damage to the company.
As a real-life example, an incident recovery team in one organization decided not to isolate the server as data had already been stolen, and such isolation would impact daily operations. A few hours later, the hacker executed ransomware on that and other servers and encrypted all the data. Ultimately, business operations were interrupted, and the organization needed more time and money for data and reputation recovery.
Additionally, documentation of actions taken and changes made during containment and eradication becomes pivotal. This documentation is a reference point for the step of “Response and recovery” and future incidents. They aid in understanding what worked effectively and what needs improvement to make the whole process faster, better, and more efficient.
To sum up, “Containment and eradication” constitute a crucial phase in the security incident response lifecycle, requiring swift action, strategic decision-making, and careful remediation efforts to minimize the impact of what already happened and limit the “pivoting points” for attackers to cause more damage.
#3 Investigation and analysis
This stage of security incident management involves systematically examining the sequence of events that led to the incident and determining its impact on systems and data.
Understanding incident scope and impact
Forensic analysis, log reviews, and comprehensive data examination are the backbone of this phase, helping to reconstruct the incident’s timeline, understand how it transpired, and identify the affected areas within the organization’s infrastructure.
Beyond understanding the sequence of events, it’s crucial to gauge the extent of the incident’s impact on systems, data integrity, and operational functionality. The assessment helps determine the incident’s criticality and guides subsequent response actions.
Importance of gathering evidence
Gathering evidence involves preserving data, logs, and any pertinent information that can offer insights into the incident’s cause, extent, and impact. Evidence collection maintains the integrity of information and serves as a foundation for potential legal actions, aiding in prosecuting perpetrators or defending against legal liabilities arising from the incident. For regulatory compliance purposes, precise documentation and evidence collection are essential to demonstrate adherence to mandated security standards and practices.
During analysis, it is also vital to collect any Indicators of Compromise (IoC) and Tactics, Techniques, and Procedures (TTPs) to adjust your detection and prevention rules and use cases to avoid such incidents in the future. Also, in some sectors like finance, for example, sharing IoCs and TTPs among organizations (even competitors) is a good practice to prevent the same attacks among different companies.
In some instances, during thorough investigation, it’s possible to attribute the incident to specific threat actors or Advanced Persistent Threats (APTs) using IoCs, along with the TTPs that were previously collected. This attribution provides critical intelligence for understanding the motives, tactics, and potential future threats such entities pose.
#4 Response and recovery
The response and recovery phase of security incident management is a coordinated and structured effort to fully mitigate the effects of an incident and restore normal operations. It is a holistic approach that encompasses technical measures, effective communication, compliance, and rapid resumption of services. The importance of this stage lies in the fact that it not only mitigates the consequences of the current incident but also strengthens the organization’s resilience to future cybersecurity challenges.
It involves a multifaceted approach beyond IT security to encompass various teams and strategies.
Establishing an incident response team
The multi-disciplinary team may include IT security professionals and representatives from HR, legal, communications, executive management, and other relevant departments. The team follows a well-defined and structured response plan to minimize the incident’s impact and return to “Business as usual” as fast as possible. This plan outlines roles, responsibilities, and actions to be taken by each team member, ensuring a coordinated effort to address the incident’s different facets. It is crucial that everyone involved in this team is aware of and well-trained regarding this plan and strictly follows it.
Mitigation and recovery
Efforts are focused on containing the incident’s impact. This might involve various actions such as restoring backups, applying security updates or patches, deploying additional security controls, and isolating compromised systems to prevent further damage.
Beyond IT, communication with stakeholders, including customers, the press, and shareholders, and fulfilling legal obligations is crucial. Transparency and effective communication are essential in managing incident fallout and protecting brand reputation.
The main goal is to restore normal operations as swiftly as possible while ensuring the systems are secure. Teams ensure that all necessary services are functional and operational post-incident. They may also perform rigorous testing to verify the integrity and functionality of systems and applications. Verification of the effectiveness of implemented measures is also crucial to guarantee that systems are adequately protected in the future.
#5 Post-incident review and improvement
“It ain’t about how hard you hit. It’s about how hard you can get hit and keep moving forward.” – Rocky Balboa
The last phase of security incident management represents a strategic moment for organizational growth and sustainability. It begins with a comprehensive and reflective examination of the incident response process itself. Teams scrutinize each previous phase to determine its effectiveness. They perform a retrospective of each incident to understand what worked well and what areas need refinement or improvement. Documenting these findings and a detailed report on the actions taken and the nuanced lessons learned becomes the basis for future use and strategic development.
The essence of this phase lies in utilizing insights gained and documented from the previous SIM phases to effect tangible improvements. Based on this evaluation, incident response protocols and plans undergo a fine-tuning process, aligning them more precisely with emerging threat landscapes and the organization’s specific needs. Security measures are recalibrated using the IoCs and TTPs collected during “Investigation and Analysis.” Additionally, the introspection fuels the refinement of training programs for staff, ensuring they are equipped with the latest knowledge and strategies to combat future threats effectively.
One of the pivotal aspects of this phase is the evolution of incident response playbooks, SIEM use cases, and the utilization of advanced Security Orchestration, Automation, and Response (SOAR) platforms. The tools are updated and enhanced, integrating insights from the incident review to refine automated response mechanisms, optimize workflow orchestration, and streamline incident resolution processes. You can also use ticketing/alerts and notifications to make the communications more effective and well-documented. This could be realized via special systems like ServiceNow, Remedy IT Service Management, or e-mails. The synergy between human expertise and automated response mechanisms bolsters the organization’s security posture. Here is the Post-incident Response Plan from the Australian Government ACSC team as a reference.
Summary
Security incident management is a structured process designed to identify, respond to, and recover from security incidents within an organization’s on-premise, hybrid, or cloud-based infrastructure. Security incidents nowadays are not about “if” but rather “when,” so there is no other option but to be prepared for them by making your security incident management very robust and effective.
In this era where cybersecurity threats continuously evolve, being prepared means more than just having reactive measures in place. It involves establishing a dynamic and effective incident response framework. Utilizing industry-standard frameworks such as the NIST Cybersecurity Framework or adhering to guidelines from ISO/IEC 27035 and ISO/IEC 27001 provides organizations with a structured approach to SIM. These frameworks offer comprehensive guidelines for identifying, responding to, and recovering from incidents, ensuring that the organization is well-prepared to navigate the complexities of modern cybersecurity challenges. Collaboration is at the core of an effective Security Incident Management strategy. By creating simple and comfortable communication among various organizational teams, a prompt and coordinated response to security threats becomes doable. This collaboration is not only horizontal, spanning different departments, but also vertical, involving everyone from frontline employees to executive leadership. For example, a well-identified and reported phishing email from a regular employee could prevent a cyber attack and save your company millions of possible losses.
The ultimate goal is not just to react to incidents but to proactively manage and mitigate their impact. Through well-implemented security incident management, organizations not only navigate incidents more effectively but also continuously enhance their resilience against the constantly evolving landscape of cyber threats. This proactive approach, coupled with a culture of vigilance and compliance with industry standards, allows organizations to not only withstand the inevitability of security incidents but also to become stronger and safer in the face of new cyber challenges.
Paladin Cloud serves as a generative AI-Powered prioritization engine that connects to existing security tools to unify, correlate and contextualize their findings. This streamlines the investigation and analysis of security incidents and improves response by prioritizing security findings. This is a very good place to start building your solid security incident management.


